Insights: Protecting the home network with Cloudflare's new (and free) 1.1.1.1 for Families, that now has malware blocking

I’ve been using Cloudflare’s free and fantastic 1.1.1.1 DNS service since it’s inception in 2018. The idea is that you configure your home network to query their DNS (at 1.1.1.1), and they promise a no-hassle, free and fast DNS query service in return. If you wish to configure your network to use 1.1.1.1, see the guidance here.
Obviously, it isn’t as simple as that. By using a centralized DNS service, one needs to put inherent trust on its provider – in this case, Cloudflare. In their privacy policy, they are transparent about the service and their ambitions.
Another aspect is performance. This is evident especially if you’re used to cloud-based SaaS services, such as Microsoft Teams, part of Office 365. Microsoft has a nicely documented set of principles for network connectivity, and to paraphrase that, DNS latency is crucial here. Microsoft has documented their peering policy, and they also offer a program called Microsoft Edge Caching Program. Thankfully, Cloudflare is peering with several access providers, including Equinix – which in return is a platform partner with Microsoft.
On a high level, using Cloudflare’s 1.1.1.1 DNS services seems like it ticks the boxes for privacy, security and latency – especially if you consider swift access to Microsoft cloud services.
Cloudflare recently announced an expansion to their 1.1.1.1 services, called 1.1.1.1 for Families and it includes two new services:
- 1.1.1.2 and 1.0.0.2 for malware blocking
- 1.1.1.3 and 1.0.0.3 for malware and adult content blocking
IPv6 is also supported, you can view the addresses here.
Again, on paper this looks very promising – a DNS service that filters out malware? Great! And filtering out adult content – especially for devices my kids use? Even better! But how, specifically is it filtered out? Who decided what gets filtered?
I couldn’t find a straight answer to this. The announcement points to Cloudflare Gateway, which I’m not familiar with. I logged in to the Cloudflare for Teams console to figure out what sort of filtering might be happening with the 1.1.1.2/1.1.1.3 DNS services.
They list SafeSearch and YouTube Restricted mode, which are both technologies from Google. In addition, one can configure security threats to block:
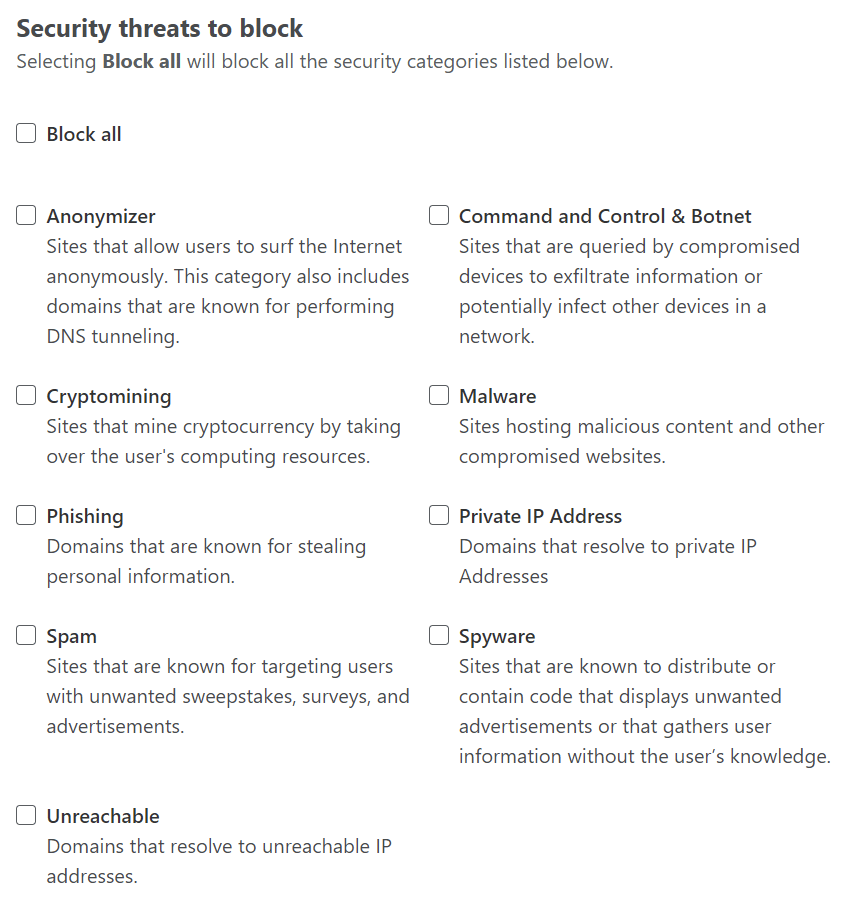
And also content categories to filter out:
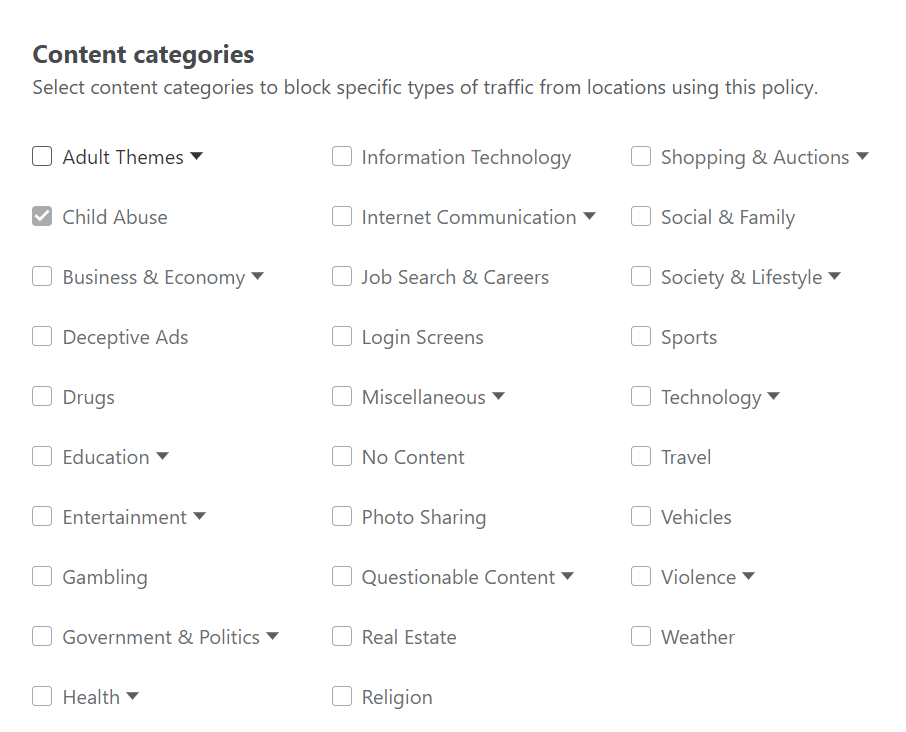
(Child abuse was selected by default, and it’s hard to disagree with.)
These controls are thus available through Cloudflare for Teams, and if the new DNS services are based on this, I’d imagine there is enough data to define what malware and adult content to block.
I’ve configured my kids’ devices to weed out certain content on Youtube and similar, but now that I have the capability to do it on infrastructure level, it’s even better. Cloudflare is promising further controls for the service at a later date, also.
I’ve now enabled the 1.1.1.2 service within my Unifi equipment, and should that prove work well, I’ll move on to 1.1.1.3 next.
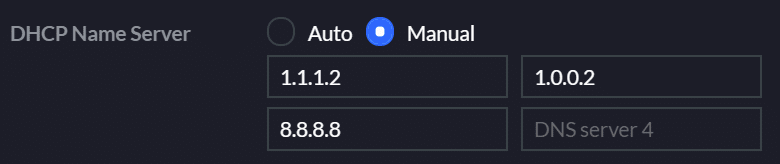
I’m still using Google’s 8.8.8.8 as a tertiary option, should Cloudflare have technical issues at any time.